Catch the fake login page before your team receives it.
Attackers exploit your trust in third-party vendors — at AI scale. Datazag fingerprints the global infrastructure surface to detect platform impersonation pre-compromise, before campaigns send. We feed it into your blocking stack as automated data, not a manual portal — and we explain why each detection fires, so defensive AI and SOC automation can act on it.
One intelligence core. Detect earlier. Delivered as data.
Brand impersonation starts with vendor impersonation.
Before attackers spoof your brand, they impersonate the platforms and vendors your business and your customers already trust — the SaaS logins, the email platforms, the suppliers.
Our April 2026 CertStream analysis found that over 85% of brand impersonations targeting the world's top 1000 brands spoofed just four platform players: Amazon, Microsoft, PayPal and Apple. That's where attackers concentrate, and that's where the infrastructure they need shows up in DNS and certificate data — before it's used against anyone.
Datazag CertStream analysis, April 2026 · 1.2M+ certificates analysed.
Start free — External Platform Threat Report
Enter your work email. We take the domain from your address, analyse its DNS and subdomains to map the platforms and vendors you actually run on — your email platform, your SaaS logins, your suppliers — then check our infrastructure feeds for spoofs targeting those exact platforms and your brand.
No asset list, no scoping call, no questionnaire. The report tells you two things you probably can't see today: which platforms expose you to impersonation, and what's already been built to exploit them. Need a report on a domain that isn't your own — a client's, a subsidiary's, a vendor's? That's a quick conversation. Talk to us.
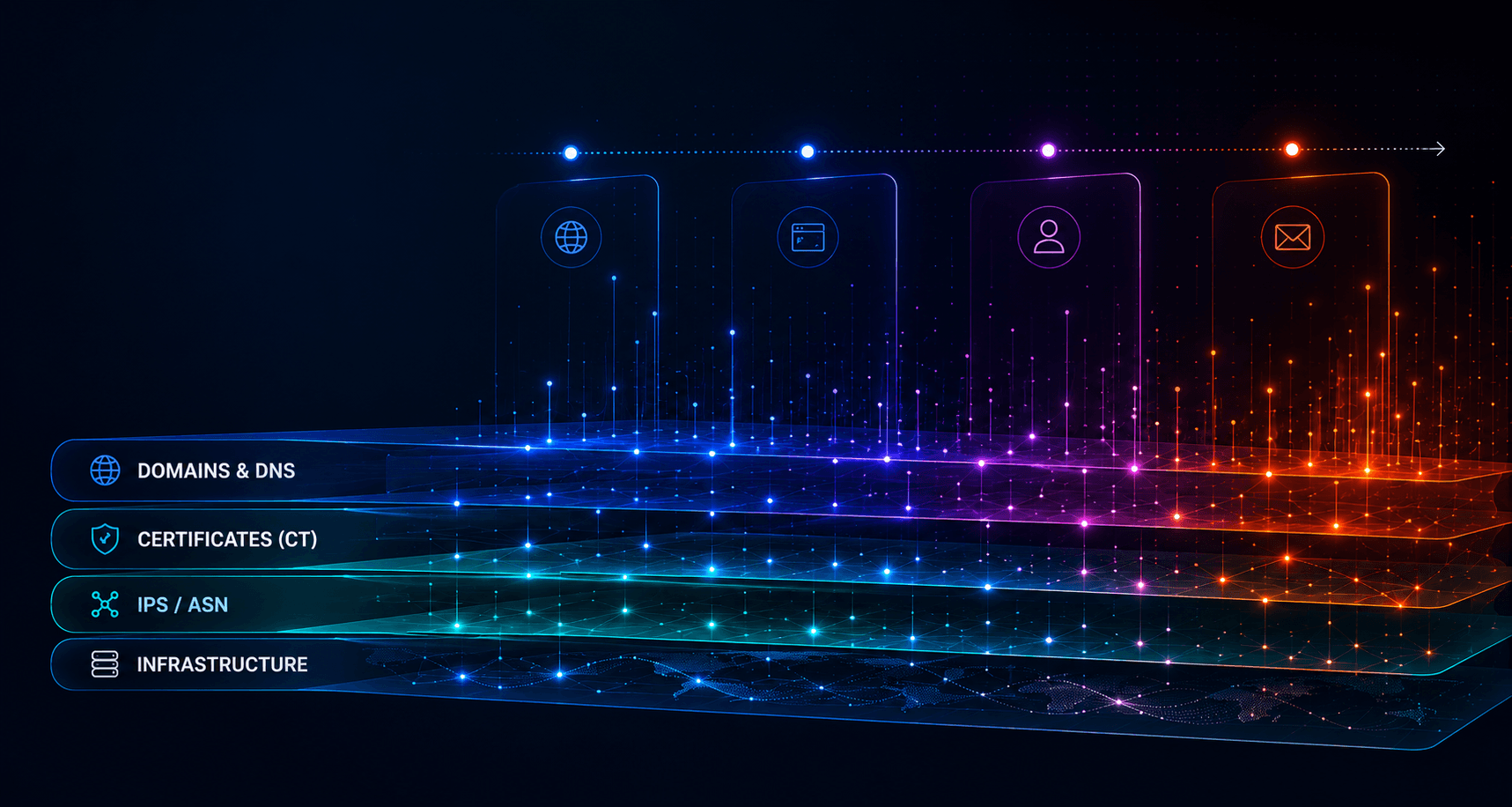
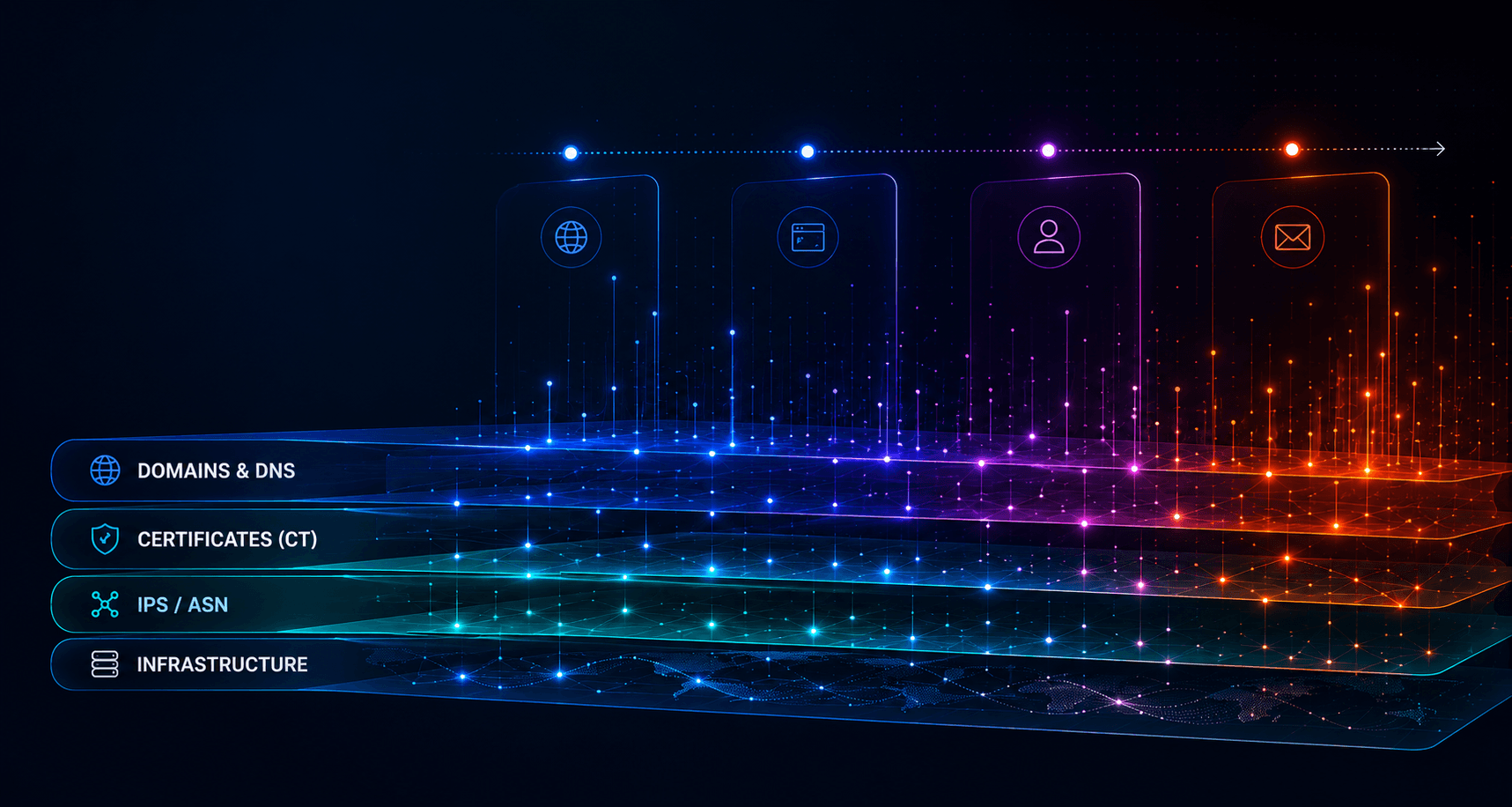
How Datazag's vendor impersonation detection works in practice.
Datazag analyses the internet infrastructure behind suspicious domains to identify impersonation attacks before they reach employees and customers.
Platform Fingerprinting
FingerprintingYour work email gives us your domain. We analyse its DNS and subdomains to map the platforms and vendors you depend on. No input from you.
Corpus Matching
MATCHINGOnce we identify your platforms, we match them to domains and IPs impersonating those brands using our continuously updated 330M-domain corpus and SSL issuance logs. We then compare each domain against the platform’s normal DNS profile and internet context — including hosting and surrounding infrastructure risk — to separate genuine spoofs from lookalikes and show the scale of the threat to your environment.
Build-Time Detection
DETECTIONImpersonation infrastructure is flagged as it's provisioned — registered, certificated, resolving — before the campaign that uses it ever launches.
Pre-Arrival Blocking
BLOCKINGWithin seconds of identifying bad infrastructure, an alert with reasons and confidence score feeds directly into your blocking stack — email security, DNS resolvers, web gateways — so the threat never reaches your inboxes, browsers or APIs.
The full 360 view. The threat outside. The trust and threat surfaces inside.
Impersonation only works when two things line up: infrastructure an attacker has built, and an attack surface that lets it land. The 360 Health Report covers both halves.
The external threat — what attackers have already built.
Platform and vendor spoofs, brand lookalikes, suspicious certificates issued against your name and your suppliers'. Drawn from the 330M-domain corpus and live infrastructure feeds; nothing required from you but a domain.
Your trust surface — how solid is the foundation you operate on.
Internet routing posture (RPKI, MANRS, IRR), ASN reputation and concentration, registrar selection and history, nameserver distribution and DNSSEC posture, domain provenance. The structural quality of the infrastructure your business runs on, scored against the rest of the namespace.
Your threat surface — how well you defend against specific attacks.
Email authentication (SPF, DKIM, DMARC, BIMI, MTA-STS), certificate authority controls (CAA), TLS hygiene (HSTS, key strength, SAN scope), subdomain integrity (dangling CNAMEs, abandoned wildcards). These configuration choices determine whether an attacker's infrastructure can land.
The external threat — what attackers have already built.
Platform and vendor spoofs, brand lookalikes, suspicious certificates issued against your name and your suppliers'. Drawn from the 330M-domain corpus and live infrastructure feeds; nothing required from you but a domain.
Your trust surface — how solid is the foundation you operate on.
Internet routing posture (RPKI, MANRS, IRR), ASN reputation and concentration, registrar selection and history, nameserver distribution and DNSSEC posture, domain provenance. The structural quality of the infrastructure your business runs on, scored against the rest of the namespace.
Your threat surface — how well you defend against specific attacks.
Email authentication (SPF, DKIM, DMARC, BIMI, MTA-STS), certificate authority controls (CAA), TLS hygiene (HSTS, key strength, SAN scope), subdomain integrity (dangling CNAMEs, abandoned wildcards). These configuration choices determine whether an attacker's infrastructure can land.
Upgrade to the full 360 view
The free report shows you the external threat. It doesn't show you your trust surface or your threat surface — and those are the halves that tell you what to do.
Add your internal trust and threat surfaces and the External Platform Threat Report becomes the full 360 Health Report: your routing, registrar and nameserver posture analysed against the threats found, your email authentication and certificate controls mapped against the attack patterns, every weak point identified, and — for IT and MSSP customers — paste-ready DNS records to close the threat-surface gaps, with provider-specific instructions.
Trust-surface findings, by their nature, often require bigger moves than DNS records can solve — registrar transfers, NS restructuring, ASN changes — and the report flags them with the context and rationale to make those decisions.
External Platform Threat Report → add internal attack surface → 360 Health Report. From there, Brand & Platform Alerts keep it current.
One engine. Three ways to put it to work.
Every Datazag product runs on the same Graph — the 330M-domain corpus, live CertStream, BGP and DNS pipelines. Pick the way you want to consume it.
360 Health Report
Platform & Brand Alerts
Datasets on cloud marketplaces
{
"event_type": "domain_impersonation",
"severity": "CRITICAL",
"timestamp": "2026-05-18T12:04:00Z",
"target_brand": "YourOrganization",
"threat_vector": {
"domain": "login-yourorganization-secure.com",
"registrar": "Eranet International",
"dns_status": "Resolving",
"mx_records": ["mail.attacker-infra.net"]
},
"action_required": "Initiate takedown workflow"
}# Connect your SOC directly to the pipeline
curl -X POST https://api.datazag.com/v1/webhooks \
-H "Authorization: Bearer dz_live_..." \
-d '{
"endpoint": "https://siem.yourdomain.com/ingest",
"events": [
"certificate_issued",
"mx_record_changed"
],
"filter": {
"target_brands": ["YourOrganization"]
}
}'Datazag is the predictive layer alongside your stack.
Datazag works with ASM, DRP, brand protection and threat intelligence — not against them. Where you've invested in any of these, Datazag is the layer that makes them work better. Where you haven't, it's the zero-input place to start.

Designed for partners.
Datazag is built for enterprises and buyers responsible for multiple organizations. The partnership shape is simple: your brand, your product, your customer relationship — Datazag intelligence inside.
Power Your Services with Datazag Intelligence.
From MSSP dashboards to M&A due diligence tools, our data feeds are designed for builders. Integrate sub-10-second infrastructure alerts and historical corpus access with just a few lines of code.
Datazag strengthens the security stack you already use.
Datazag works alongside ASM, DRP, SIEM, XDR, and threat intelligence platforms to identify malicious infrastructure before attacks reach users, inboxes, or endpoints.
The World’s Infrastructure, updated by the minute.
Beyond simple blacklists. Access a living, breathing map of 330M+ active domains, global SSL issuances, and IP reputations. Our corpus is the foundational layer for modern threat modelling and AI-driven defense.
Comprehensive DNS records
We don't just track A-records. Our corpus includes historical and real-time logs for every DNS records including MX, TXT (SPF/DKIM), CNAME, PTR, and SRV records across the global IPv4 and IPv6 space. We drill down from PTR and CNAME records, providing the "paper trail" needed for deep forensic investigations and attribution.
Hourly Risk Scoring
Every entity in our 330M domain corpus is re-evaluated every 60 minutes for dynamic reputation intelligence. We calculate risk scores based on infrastructure shifts, registrar reputation, and SSL staging patterns. Most datasets are static or updated weekly. Hourly scoring allows MSSPs to automate "Step-up" authentication or blocking based on live volatility.
Native Annotation
Every record is tagged with contextual metadata—identifying platform targets (e.g., "M365-Impersonation-Likely"), mail box provider, industry verticals, location and infrastructure intent. This saves your developers from having to build their own classification logic. The "meaning" of the data is baked into the JSON payload.
Mapped Against Internet Infrastructure
We map domains directly to their underlying ASN, BGP prefixes, and IP subnets. See the "neighbourhood" a domain lives in to identify malicious hosting clusters. This allows for "Guilt by Association" detection. If a new domain is registered in a known "bad neighbourhood," you know before the first packet is sent.
Designed for partners.
Datazag is built for enterprises and buyers responsible for multiple organizations. The partnership shape is simple: your brand, your product, your customer relationship — Datazag intelligence inside.